Reliance Communications Asset Freeze Dispute
This article is written by Nameera Meraj, of Aligarh Muslim University. Recently, Reliance Communications dispute has brought renewed attention to the evolving interface between insolvency law, arbitration, and sector-specific regulation
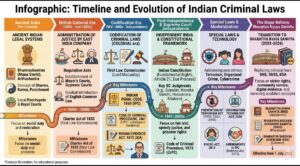
Infographic: Timeline and Evolution of Indian Criminal Laws
This Article is written by Nameera Meraj, Aligarh Muslim University. Indian criminal law has developed over centuries, shaped by changing political structures, social needs, and evolving notions of justice. What began

Case Studies and Practical Implications under the BSA
This article is written by Aditya Shankar Rawani, Radha Govind University. This article makes a critical analysis of the case studies and implications on the practice under the umbrella of BSA
Live-in Relationship and Social Morality
This article is written by Aditya Shankar Rawani, Radha Govind University. This article basically revolves around and explores the social behaviour of individuals in society towards live-in relationships in the era
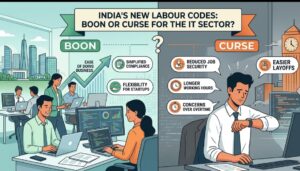
New Labour Codes for India’s IT Sector: Boon or Curse?
This article is written by Jeyashri R, a student at Government Law College, Madurai, Tamil Nadu. This article examines the new Labour Codes applicable to the Information Technology (IT) Sector.

Lex Situs & Movables: Is Location Still Relevant in a Virtual Economy?
This article is written by Manvika Kalia of Lovely Professional University, Punjab. Few doctrines in private international law have the staying power of lex situs, the principle that rights over

